Automatic login with SSH
Introduction
If you use ssh to connect to remote servers, you should not use a password to log in to them, and instead configure a key to log in. There are exceptions to this, but even then it is good to have a key that will be used to improve security and allow you to run scripts against the remote site.
Benefits
The first benefit is improved security. By not having a password that can be used for an account, that makes the account much safer. An attacker can no longer brute force or otherwise try to guess your password in order to log in as you.
Scripts are the second benefit. Not having to enter the password means you can automate tasks through ssh and not have to worry about how the password is supplied or saved for the script to run.
How to configure SSH from a Mac
For this example, let’s call the computer that you are going to log in from the client and the computer you are going to log in to the server. (NOTE: This could have just as easily been called computer A and B, nothing makes the client or server special, it is just a name to make it clear what machine you are doing what on.)
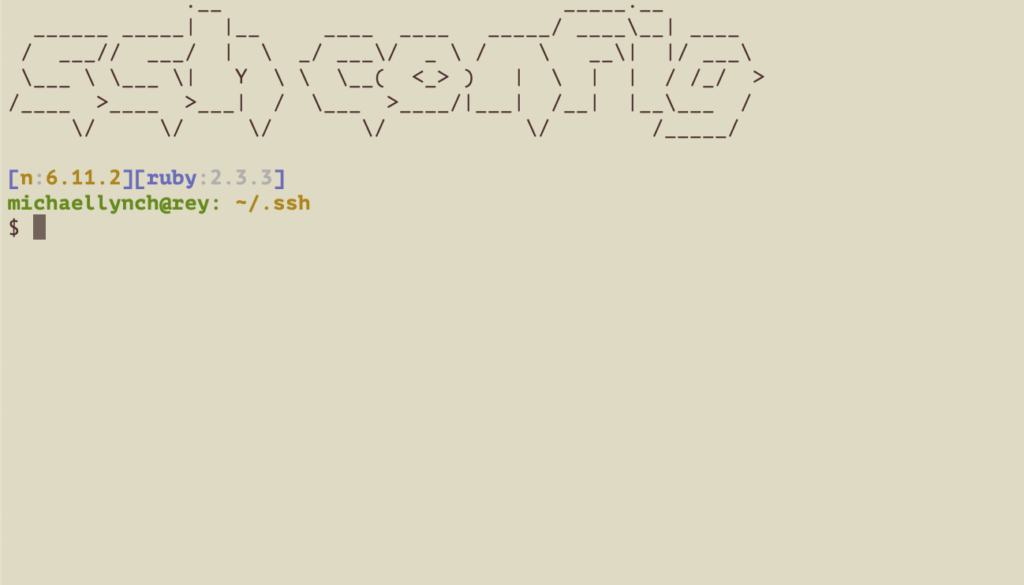
Begin by opening a terminal on the computer you want to use as your client, in Mac OSX, that would be opening the terminal.app (Applications -> Utilities -> Terminal.app).
To create a key, use ssh-keygen.
$ ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/Users/mike/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in id_rsa.
Your public key has been saved in id_rsa.pub.
The key fingerprint is:
SHA256:<fingerprint>
The key's randomart image is:
+---[RSA 2048]----+
| .... Bo.+ |
+----[SHA256]-----+
If you do not already have an ~/.ssh directory on your server, you should create it now. You can create one by connecting to it and running the commands or by using ssh from the client. (NOTE: If the directory already exists, these commands are harmless.)
$ ssh <user>@<server> mkdir -p .ssh
<user>@<server>'s password:
The authenticity of host '10.0.0.2)' can't be established.
ECDSA key fingerprint is SHA256:xyz.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '10.0.0.2' (ECDSA) to the list of known hosts.
Now we are going to add the client’s key to the server. To do this we append the key to a file in the servers .ssh directory called ‘authorized_keys‘.
$ cat .ssh/id_rsa.pub | ssh <user>@<server> 'cat >> .ssh/authorized_keys'
<user>@<server>'s password:
That is the last step in the process, you should now be able to log in without a password. To try it, simply try:
$ ssh <user>@<client>
Conclusion
This same process can be used multiple times from any machine that you connect to with ssh, including AWS EC2 servers that you maintain, local servers, etc. Finally, you may want to remove the password login for a user once this is set up, this can be dangerous, if you lose your key, you will not be able to log in once the password is turned off, so keep backups of your keys.
Hope that helps you!